Uncover Undetected Risks
Assess your risk and measure your exposure to threats that may have evaded your existing security solutions.
Scan your endpoints, mailboxes, cloud resources, and any other internet-facing assets within your environment to understand your true cyber risk posture.
Low friction Zero cost Rapid time to value
Section 1 - Column 3. Praesent non velit ut libero
condimentum pulvinar sed vitae tellus.
Vestibulum
id tristique elit. Suspendisse posuere rutrum
sodales. Nam id elit ac sem iaculis lacinia
posuere vitae metus.
Section 1 - Column 4. Praesent non velit ut libero
condimentum pulvinar sed vitae tellus.
Vestibulum
id tristique elit. Suspendisse posuere rutrum
sodales. Nam id elit ac sem iaculis lacinia
posuere vitae metus.
Understand Use Cases
Free assessments delivering fast value, solving key challenges and pain points.
View infographic →
Section 2 - Column 3. Praesent non velit ut libero
condimentum pulvinar sed vitae tellus.
Vestibulum
id tristique elit. Suspendisse posuere rutrum
sodales. Nam id elit ac sem iaculis lacinia
posuere vitae metus.
Section 2 - Column 4. Praesent non velit ut libero
condimentum pulvinar sed vitae tellus.
Vestibulum
id tristique elit. Suspendisse posuere rutrum
sodales. Nam id elit ac sem iaculis lacinia
posuere vitae metus.
Explore our free cyber risk assessments

Cloud Security Posture

External Attack Surface

Microsoft Exchange Online/Gmail

At-Risk Endpoint

Phishing Simulation

Vulnerability Analysis
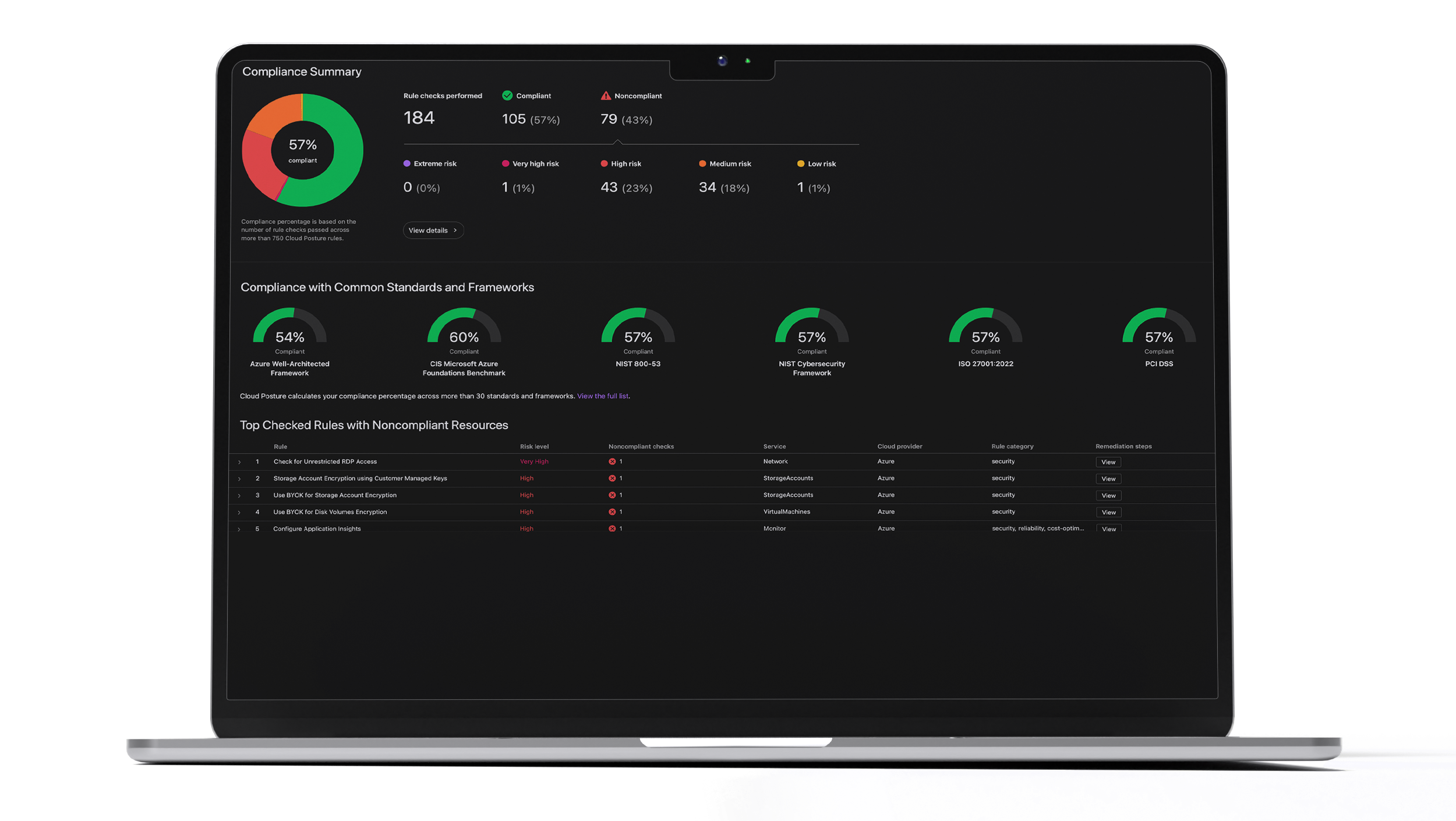
Cloud Security Posture Assessment
Scan your organization's cloud infrastructure to identify misconfiguration, compliance, and security risks based on common standards and practices.
External Attack Surface Assessment
Enter your organization's domain to scan and discover risks and vulnerabilities hiding in your internet-facing assets.

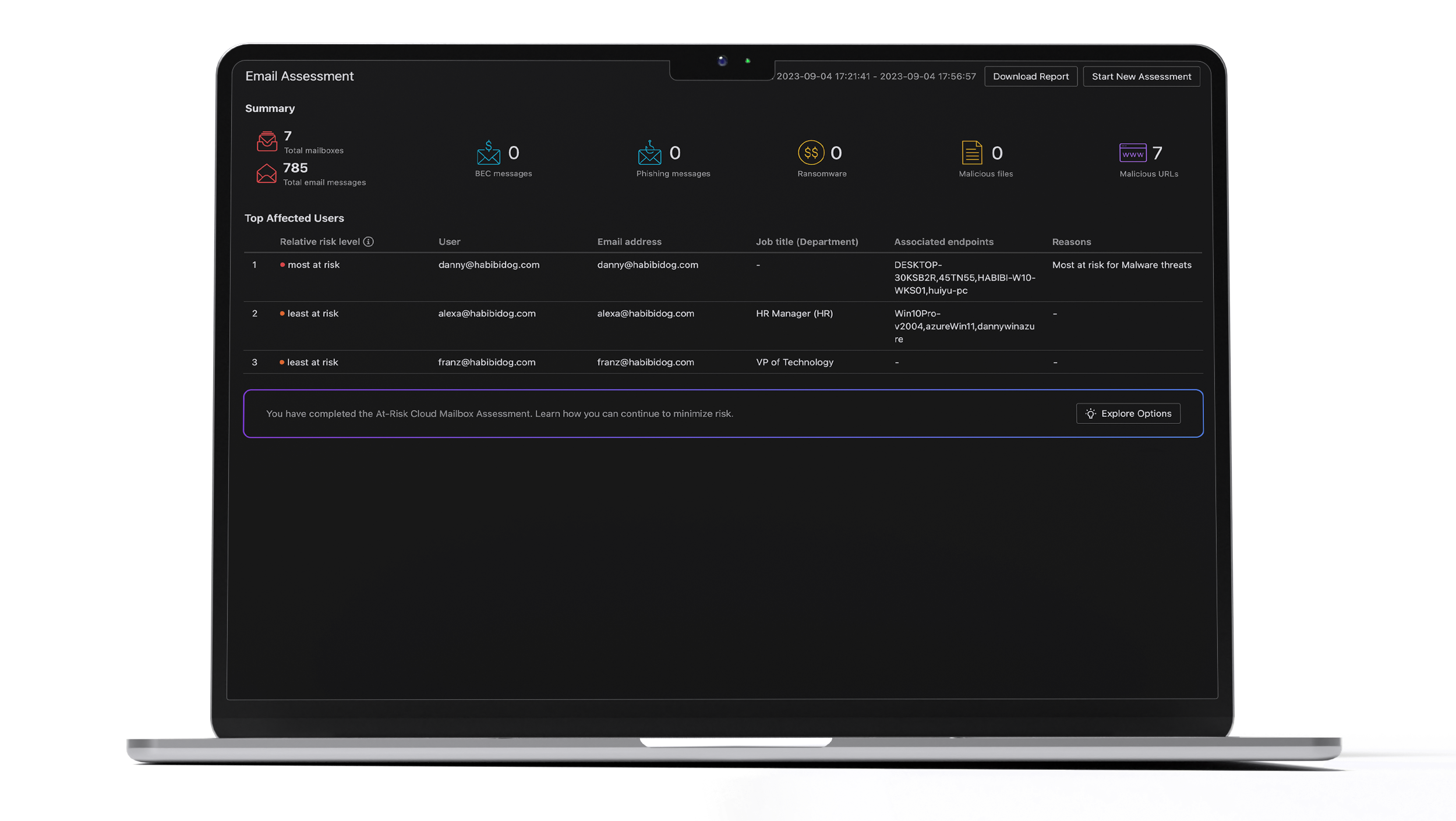
Microsoft Exchange Online/Gmail Assessment
Uncover business email compromise (BEC) attempts, phishing attacks, ransomware, malicious files, or URLs in messages from the last 15-30 days.
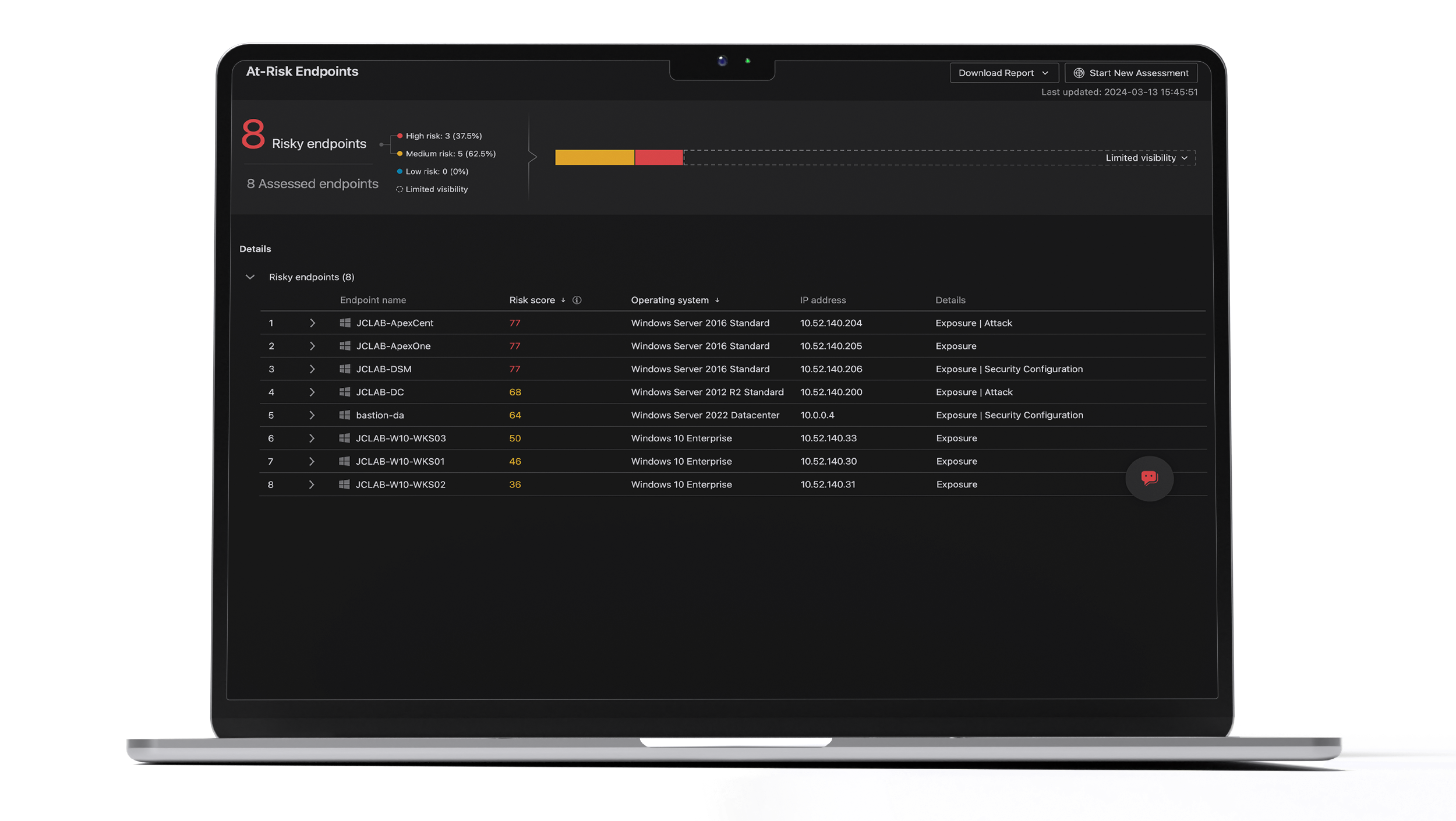
At-Risk Endpoint Assessment
Scan high-profile endpoints across your organization for file-based threat indicators collected from global intelligence sources.
Phishing Simulation
Choose a phishing email template and monitor results for insight into the human risk across your organization.

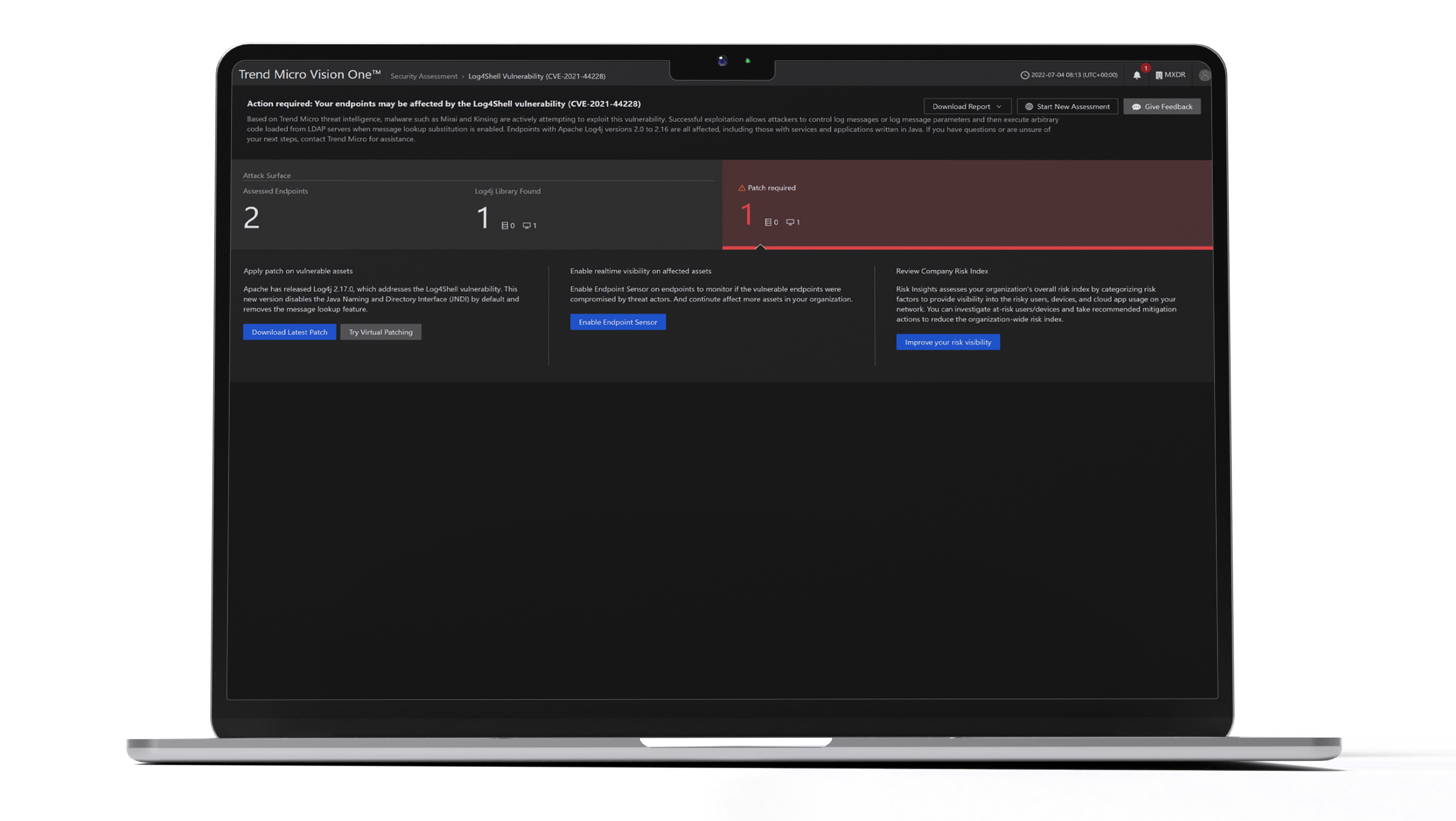
Vulnerability Analysis Assessment
Scan your endpoints to discover your exposure and determine if you've been impacted by the latest threats.
Section 3 - Column 2. Praesent non velit ut libero
condimentum pulvinar sed vitae tellus.
Vestibulum
id tristique elit. Suspendisse posuere rutrum
sodales. Nam id elit ac sem iaculis lacinia
posuere vitae metus.
Section 3 - Column 3. Praesent non velit ut libero
condimentum pulvinar sed vitae tellus.
Vestibulum
id tristique elit. Suspendisse posuere rutrum
sodales. Nam id elit ac sem iaculis lacinia
posuere vitae metus.
Section 3 - Column 4. Praesent non velit ut libero
condimentum pulvinar sed vitae tellus.
Vestibulum
id tristique elit. Suspendisse posuere rutrum
sodales. Nam id elit ac sem iaculis lacinia
posuere vitae metus.
Section 4 - Column 2. Praesent non velit ut libero
condimentum pulvinar sed vitae tellus.
Vestibulum
id tristique elit. Suspendisse posuere rutrum
sodales. Nam id elit ac sem iaculis lacinia
posuere vitae metus.
Section 4 - Column 3. Praesent non velit ut libero
condimentum pulvinar sed vitae tellus.
Vestibulum
id tristique elit. Suspendisse posuere rutrum
sodales. Nam id elit ac sem iaculis lacinia
posuere vitae metus.
Section 4 - Column 4. Praesent non velit ut libero
condimentum pulvinar sed vitae tellus.
Vestibulum
id tristique elit. Suspendisse posuere rutrum
sodales. Nam id elit ac sem iaculis lacinia
posuere vitae metus.
Questions or need assistance? Please contact our Technical Support team.
Our Trend Vision One platform supports the following desktop browsers (not officially supported on Android™/iOS devices):
Google Chrome™ | Mozilla Firefox| Microsoft Edge
Section 5 - Column 2. Praesent non velit ut libero
condimentum pulvinar sed vitae tellus.
Vestibulum
id tristique elit. Suspendisse posuere rutrum
sodales. Nam id elit ac sem iaculis lacinia
posuere vitae metus.
Section 5 - Column 3. Praesent non velit ut libero
condimentum pulvinar sed vitae tellus.
Vestibulum
id tristique elit. Suspendisse posuere rutrum
sodales. Nam id elit ac sem iaculis lacinia
posuere vitae metus.
Section 5 - Column 4. Praesent non velit ut libero
condimentum pulvinar sed vitae tellus.
Vestibulum
id tristique elit. Suspendisse posuere rutrum
sodales. Nam id elit ac sem iaculis lacinia
posuere vitae metus.